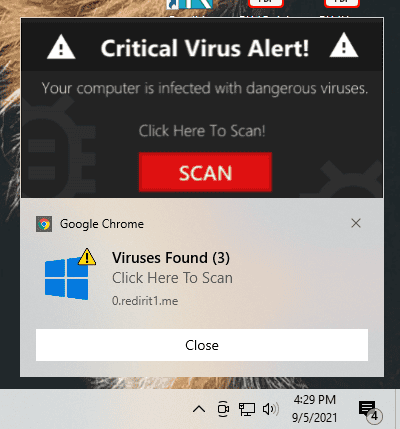
Protect Your Business from Chrome notification Spam and Phishing Threats As a small business owner or a busy professional, you’ve likely experienced...
Stop Google Chrome Notification Spam For BusinessNavigating PCI DSS 4.0 Compliance in 2024: Essential Steps for Small Business Security and Success Small businesses are facing a growing number of cyber...
Pci Dss 4 0 Compliance And Small BusinessLearn how to comply with SEC cybersecurity disclosure rules in 2024. This guide covers material incident reporting, governance practices, and risk management strategies to help your business stay secure and compliant....
Sec Cybersecurity Disclosure Compliance 2024Data breaches have become a persistent and costly threat to businesses of all sizes. The consequences of a data breach can be devastating, ranging from financial losses and legal penalties to reputational damage. As organizations scramble to fortify their data security, it's crucial to understand the most common causes of data breaches, so that companies can effectively mitigate risks. This article...
Most Common Causes Of Data Breaches Understanding And Preventing Security VulnerabilitiesHealthcare breaches pose serious risks to patient privacy, operational continuity, and regulatory compliance. This article delves into the causes, impacts, and actionable strategies to safeguard healthcare organizations from cyber threats....
Understanding The Impact Of Healthcare BreachesIn a decisive move to fortify America's maritime assets, the White House has issued an Executive Order aimed at enhancing the cybersecurity of the nation's ports. This strategic action is designed to safeguard these crucial gateways from potential cyber threats, particularly those emanating from Chinese technology embedded within cargo cranes....
Securing American Ports A Bold Move Against Cyber ThreatsIn a startling revelation, Microsoft confirmed that the Russia-linked group Midnight Blizzard has compromised its employee email accounts since November 2023. This breach, involving a group also linked to the SolarWinds hack, underscores the escalating cyber warfare landscape. #MidnightBlizzard #MicrosoftCybersecurity #RussiaLinkedHack #MicrosoftHacked...
Midnight Blizzard Breach Unraveling Microsofts Latest Cybersecurity ChallengeSafeguarding Client Data in Finance: Essential Cybersecurity Steps Before Tax Season
As tax season approaches, businesses, especially CPA firms, traders, and bankers, must prioritize securing their computer networks to protect the highly sensitive client data they handle. This is not only a matter of safeguarding their reputation but also of complying with increasingly stringent regulations.
As businesses approach the end of the year, preparing for cybersecurity challenges in the coming year is paramount. Recent developments and trends highlight key areas where focus and improvement are essential. 1. Adapting to New SEC Cybersecurity Rules The Securities and Exchange Commission (SEC) has introduced new cybersecurity rules that necessitate a change in how businesses handle risk management, governance, and incident...
End Of Year Preparations For Businesses For The New YearBusinesses Need Firewalls, in all jurisdictions. In today’s digital-first business environment, network security is not just a technical requirement but a crucial aspect of ensuring ongoing productivity and safeguarding intellectual property. One fundamental component of this security infrastructure is the network firewall. Not only does it protect against external threats but also plays a vital role in maintaining an efficient and...
Network Firewalls 201 Cmr 17