IT Insights & News
Managed IT, Cybersecurity & Compliance Resources
When AI Negotiates Against You: A HIPAA Migration Lesson
Trave Harmon – May 26, 2026
Why Your Cyber Insurance Policy May Already Be Void: The Travelers Warning
Trave Harmon – May 1, 2026
The Claude AI Case Study: 38 Projects, $767K in Value, One Person
Trave Harmon – April 25, 2026
In 50 calendar days, one person completed 38 projects using Claude AI — delivering $767,983 in first-year value with a 136,338% ROI. Here's how.
Read More
Why Your External Network Hardware Fails When Weather Turns
Trave Harmon – February 7, 2026
Last week, two wireless internet service providers called me about the same problem. Their external network hardware was failing. Not gradually. Completely.One was on Cape Cod. The other in upstate...
Read More
Why Your Information Security Policy Is Already Outdated
Trave Harmon – January 30, 2026
I review client documentation as part of my fractional CTO work. In 2026, I started seeing the same problem everywhere: companies using security policy templates that stopped working years ago.They...
Read More
Why CMMC Compliance Is Forcing Managed IT Providers to Rethink Physical Security
Trave Harmon – January 20, 2026
November 2025 changed everything for managed IT providers working with defense contractors.That's when the Department of Defense officially began CMMC enforcement through defense contracts. After...
Read More
Zero Trust Security and Why Triton Technologies Avoids Whitelisting
Trave Harmon – November 18, 2025
Rhode Island has updated its data breach notification law to require faster disclosure, stricter reporting, and full consumer protection. If your business or agency handles resident data, this law applies to you. Learn what changed, why it matters, and how to stay compliant in 2025.
Read More
Secure and Simple Logins with Duo and YubiKey
Trave Harmon – August 5, 2025
Rhode Island has updated its data breach notification law to require faster disclosure, stricter reporting, and full consumer protection. If your business or agency handles resident data, this law applies to you. Learn what changed, why it matters, and how to stay compliant in 2025.
Read More
Rhode Island Data Breach Law Updated for 2025
Trave Harmon – June 17, 2025
Rhode Island has updated its data breach notification law to require faster disclosure, stricter reporting, and full consumer protection. If your business or agency handles resident data, this law applies to you. Learn what changed, why it matters, and how to stay compliant in 2025.
Read More
Massachusetts Data Breach Notification Law Updated for 2025
Trave Harmon – June 11, 2025
Massachusetts has updated its data breach notification law with stricter requirements for businesses that collect or store personal data. This update demands faster reporting, confirms who must comply, and outlines what every business needs to do right now to stay protected and avoid penalties. Triton Technologies breaks it down.
Read More
IRS Publication 4557: How Small Businesses Can Protect Taxpayer Data with Confidence
Trave Harmon – June 6, 2025
Discover how AWS Snapshots can quickly restore your systems during a crisis. Learn from Triton Technologies how to effectively use snapshots for disaster recovery.
Read More
Secure Your Domain by Transferring to Cloudflare
Trave Harmon – June 5, 2025
New data privacy laws are now active across eight states. If your business collects or processes personal data, this is not optional. Triton Technologies breaks down what small businesses must do to stay compliant, protect customer trust, and avoid penalties.
Read More
Data Privacy in 2025
Trave Harmon – June 2, 2025
New data privacy laws are now active across eight states. If your business collects or processes personal data, this is not optional. Triton Technologies breaks down what small businesses must do to stay compliant, protect customer trust, and avoid penalties.
Read More
Email Authentication for Business: Why SPF, DKIM, and DMARC Matter
Trave Harmon – May 21, 2025
Every business needs to implement SPF DKIM and DMARC as essential measures for protecting email integrity. Email functions as the essential communication...
Read More
Why Cloud Infrastructure Is the Smart Move for Small Businesses in 2025
Trave Harmon – May 17, 2025
Spring time is the worst time... for networks. Spring in the Northeast brings more than blooming flowers; it ushers in unpredictable weather patterns...
Read More
Why Ransomware Keeps Targeting Small Businesses and What You Can Do About It
Trave Harmon – May 16, 2025
Ransomware Is No Longer Just a Big Business Problem Most headlines talk about massive companies and data breaches, but the real danger is much closer to...
Read More
Cybersecurity Threats Small Businesses Can No Longer Ignore
Trave Harmon – May 7, 2025
Small businesses are facing a rising wave of cyberattacks. Learn why phishing, ransomware, and compliance failures are costing companies thousands—and what you can do today to protect your business.
Read More
Protecting Your Cloud Foundation: Important Security Updates for Our AWS Partners
Trave Harmon – April 7, 2025
Protecting Your Cloud Foundation: Essential AWS Security for Small Businesses At Triton Technologies, your trusted AWS partner, we understand the pivotal...
Read More
How Cloud Computing Lowers IT Costs and Boosts Business Efficiency
Trave Harmon – February 13, 2025
The Rising Costs of On-Premises IT Infrastructure The costs of supporting traditional in-office IT systems are rising exponentially today. The financial...
Read More
Project Axiom
Trave Harmon – February 5, 2025
Triton Technologies has redefined IT service delivery with Project Axiom, an AI-driven system that slashes ticket response times from 15 minutes to just 5 seconds. By integrating ConnectWise Manage with a vast Confluence knowledge base, our in-house AI automates ticket analysis, technician assignment, and knowledge retrieval—eliminating delays and inefficiencies. This...
Read More
Protecting Your Business from Fake Domain Renewal Scams
Trave Harmon – December 26, 2024
Fake domain renewal scams have become a pervasive threat, targeting businesses with fraudulent notices designed to exploit trust and urgency. This post explores how these scams work, highlights red flags, and provides actionable tips to safeguard your company’s online presence.
Read More
Rhode Island RIBridges Hack: How Penetration Testing and Encryption Could Have Prevented It
Trave Harmon – December 17, 2024
Rhode Island's RIBridges system suffered a ransomware attack by Brain Cipher, exposing thousands of residents’ sensitive data. Learn how penetration testing, encryption, and proactive cybersecurity measures could have prevented this breach and safeguarded public trust.
Read More
Lessons from Krispy Kreme’s Cybersecurity Incident: Protecting Your Business from Digital Threats
Trave Harmon – December 15, 2024
Krispy Kreme recently faced a cybersecurity breach impacting its online ordering systems nationwide. This incident highlights the growing need for small and medium businesses to implement robust cybersecurity measures to safeguard their operations and customer trust.
Read More
Transitioning to Sophos XGS Firewalls: Enhancing Security for Modern Businesses
Trave Harmon – December 12, 2024
Sophos is retiring its XG firewalls, making way for the more advanced XGS series. With features like Xstream Architecture, enhanced threat protection, and seamless AWS integration, the XGS series provides cutting-edge security and performance. Learn how Triton Technologies supports this transition.
Read More
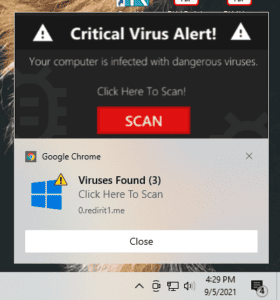
Why Google Chrome Notifications Are a Growing Problem for Businesses—and How to Fix It
Trave Harmon – December 9, 2024
Protect Your Business from Chrome notification Spam and Phishing Threats As a small business owner or a busy professional, you’ve likely experienced...
Read More
PCI DSS 4.0 Compliance and Small Business
Trave Harmon – November 25, 2024
Navigating PCI DSS 4.0 Compliance in 2024: Essential Steps for Small Business Security and Success Small businesses are facing a growing number of cyber...
Read More
Navigating SEC Cybersecurity Disclosure Rules: A Comprehensive Guide
Trave Harmon – November 17, 2024
Learn how to comply with SEC cybersecurity disclosure rules in 2024. This guide covers material incident reporting, governance practices, and risk management strategies to help your business stay secure and compliant.
Read More
How MSPs Deliver IT Solutions for the Insurance Industry
Trave Harmon – November 1, 2024
In a competitive landscape where global commercial insurance rates have recently seen their first decline in seven years, insurers face increasing pressure to optimize costs and deliver top-notch services to clients. This change, tracked by Marsh’s Global Insurance Market Index, points to an industry where insurers must find ways to...
Read More
Most Common Causes of Data Breaches: Understanding and Preventing Security Vulnerabilities
Trave Harmon – October 18, 2024
Data breaches have become a persistent and costly threat to businesses of all sizes. The consequences of a data breach can be devastating, ranging from financial losses and legal penalties to reputational damage. As organizations scramble to fortify their data security, it's crucial to understand the most common causes of...
Read More
Essential Steps to Ensure NIS2 Compliance in 2024
Trave Harmon – October 11, 2024
As the NIS 2 Directive compliance deadline approaches in October 2024, businesses across the globe must act swiftly to ensure they meet the new cybersecurity standards outlined in the updated directive. With the cybersecurity threat landscape evolving, Triton Technologies is committed to helping organizations navigate these changes and prepare for...
Read More