Addressing Internal Cybersecurity Threats in Your Business: Why It's Crucial
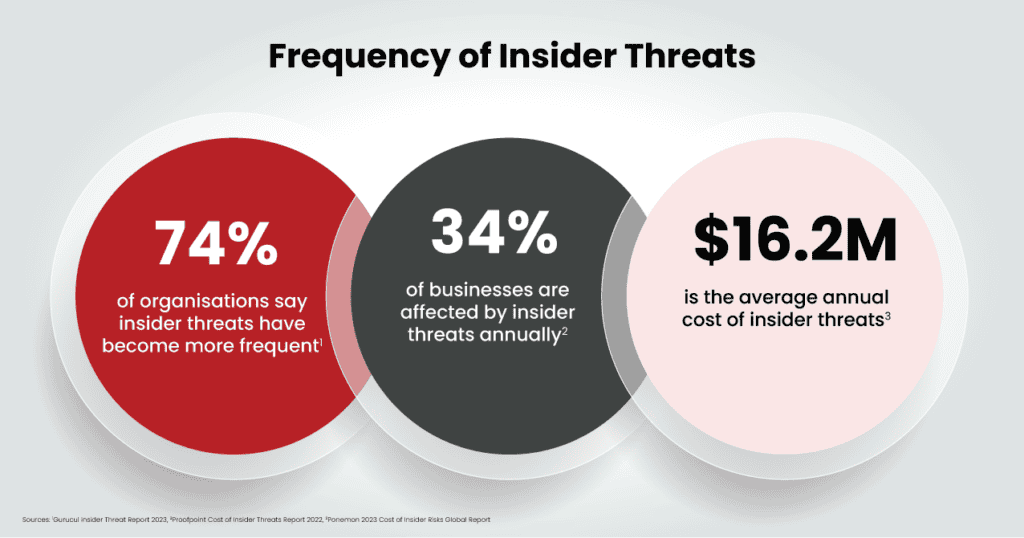
When we think of cybersecurity threats, many of us imagine skilled hackers or malicious cybercriminals attacking from the outside. However, a significant and often overlooked threat to business security can come from within the organization itself. Employees—whether intentionally malicious or unintentionally careless—can pose a serious risk to your company’s sensitive data and systems. Cyberattacks by disgruntled employees, whether current or former, are not as rare as one might think. It’s essential to recognize that internal cybersecurity threats can be just as damaging as those from external attackers.
The impact of falling victim to internal cybercrime can be devastating. Not only can it lead to direct financial losses through things like ransom demands or legal penalties, but it can also severely damage your company’s reputation, erode customer trust, and disrupt daily operations. The consequences are far-reaching, affecting your bottom line and long-term viability.
To protect your business from these threats, adopting a proactive, layered approach to cybersecurity is critical. Here’s how businesses can effectively address internal cybersecurity risks:

Acknowledge the Risk from Within
The first step in mitigating internal cybersecurity threats is recognizing that employees—whether intentionally or not—can be a security risk. This is where the concept of “trust but verify” comes into play. While trust is essential for fostering a positive workplace culture, it’s equally important to have measures in place that verify and monitor employees’ actions in relation to sensitive data and IT systems.
Implement policies that limit access to critical systems and data based on role and necessity. By ensuring employees only have access to the information they truly need, you reduce the chance of an internal breach, whether it’s accidental or malicious.
Educate Employees on Cybersecurity Best Practices
An informed workforce is one of the best defenses against internal security breaches. Regular employee training on cybersecurity is crucial to prevent unintentional errors that could lead to data compromise. Employees should understand the risks associated with:
- Sharing one-time passwords (OTPs)
- Using unsecured public Wi-Fi for business operations
- Leaving devices unattended in public spaces
- Visiting suspicious websites or downloading unknown attachments
- Falling victim to phishing emails or scams
By educating your staff on these risks, you empower them to make safer decisions, thereby reducing the likelihood of security breaches caused by human error.
Implement Ethics and Security Awareness Training
In addition to technical training, businesses should also invest in ethics and security awareness programs. Employees should be made aware of what is considered ethical and acceptable behavior in the workplace, particularly when handling sensitive information. Training sessions should cover the severe consequences of unethical actions, such as data theft or deliberate sabotage of systems.
When employees understand the full ramifications of breaching security protocols—both for the business and for themselves—they are more likely to adhere to the security guidelines and policies set forth by the organization.
Conduct Surprise Audits and Monitoring
Cybersecurity is not something that can be set and forgotten—it requires constant vigilance. To ensure employees are following the established security protocols, it’s essential to conduct surprise audits and assessments regularly. These audits will help identify potential vulnerabilities and gaps in security that may have been overlooked.
Unannounced audits also help to reinforce the idea that the organization is always monitoring compliance, which can deter employees from engaging in risky behaviors that could lead to breaches. In addition to audits, continuous monitoring of network activity, system logs, and access controls is vital in detecting any abnormal behavior early on.
Invest in Advanced Cybersecurity Tools and Infrastructure
While employee training is crucial, it should not be your only line of defense. Implementing advanced cybersecurity tools can provide an additional layer of protection. These tools help detect and prevent security threats, both from internal and external sources.
Key cybersecurity infrastructure to consider includes:
- Firewalls: To block unauthorized access and traffic.
- Network monitoring systems: To detect unusual or suspicious activity within your network.
- Anti-malware programs: To protect against viruses, ransomware, and other malicious software.
- Access management systems: To control employee access based on roles, ensuring that sensitive data is only accessible to those who need it.
By using these tools, you can ensure that your systems are continuously protected against both internal and external threats.
Discover our IT Solutions for Your Industry
Worcester’s Top Managed Service Provider
Partner with a Managed Service Provider (MSP)
For businesses looking for a comprehensive approach to cybersecurity, partnering with a Managed Service Provider (MSP) specializing in cybersecurity can be invaluable. An MSP can offer expert guidance on developing a secure IT environment, implement the latest security tools, and monitor your network for potential threats 24/7.
Additionally, an MSP can assist with employee training, audit procedures, and cybersecurity strategy development. With a dedicated team focused on safeguarding your data, you can rest easy knowing that your company is protected from both internal and external risks.
Safeguard Your Business with Proactive Internal Security Measures
Internal cybersecurity threats are often underestimated, yet they can be just as destructive as external attacks. By recognizing the risks, educating employees, implementing robust security policies, and investing in the right tools, businesses can significantly reduce the chances of a data breach from within.
Remember, a comprehensive approach to cybersecurity includes not just technology and policies but also a culture of awareness and responsibility among employees. With the right measures in place, your business can navigate the complexities of cybersecurity, ensuring that both external and internal threats are mitigated effectively.
Explore our Managed Service Offerings
Worcester’s Top Managed Service Provider