In 50 calendar days, one person completed 38 projects using Claude AI — delivering $767,983 in first-year value with a 136,338% ROI. Here's how....
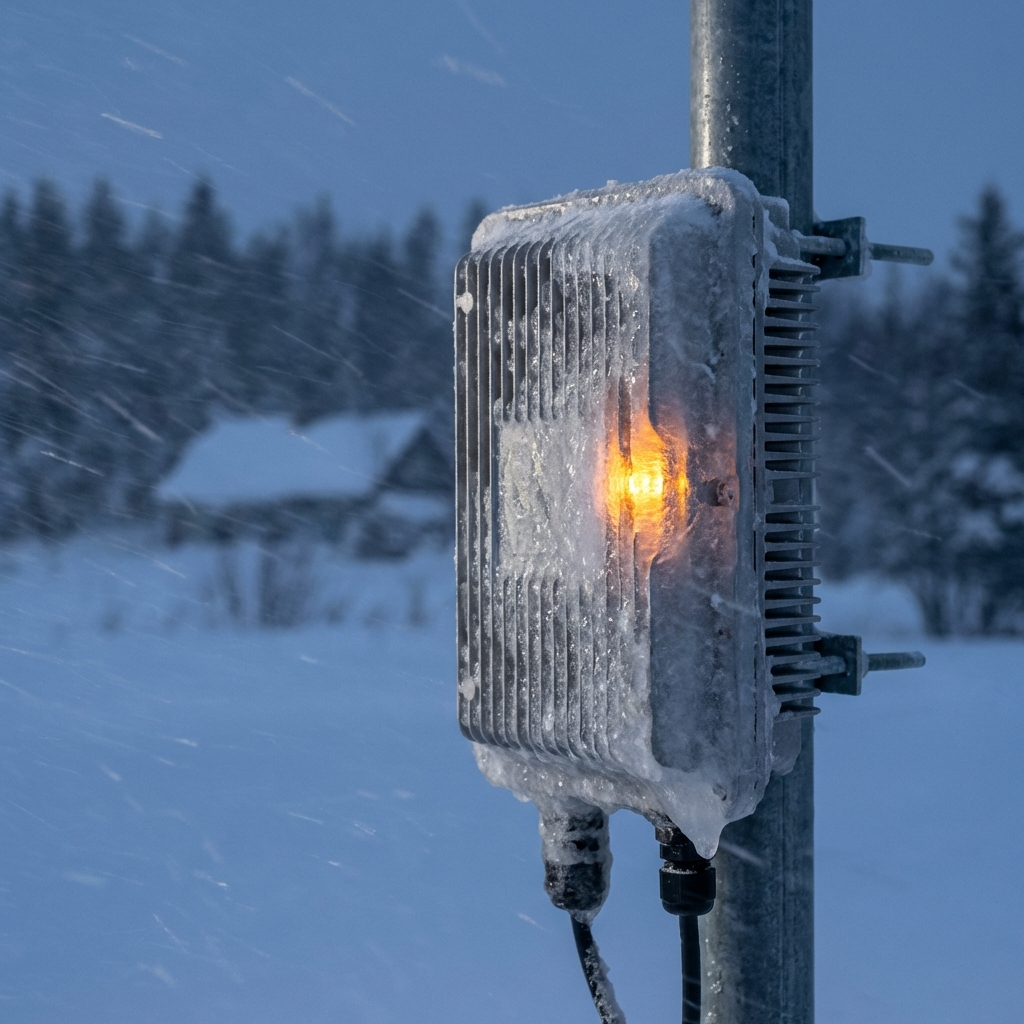
The Claude Ai Case Study 38 Projects 767k In Value One PersonLast week, two wireless internet service providers called me about the same problem. Their external network hardware was failing. Not gradually. Completely.One was on Cape Cod. The other in upstate...
Why Your External Network Hardware Fails When Weather TurnsI review client documentation as part of my fractional CTO work. In 2026, I started seeing the same problem everywhere: companies using security policy templates that stopped working years ago.They...
Why Your Information Security Policy Is Already OutdatedNovember 2025 changed everything for managed IT providers working with defense contractors.That's when the Department of Defense officially began CMMC enforcement through defense contracts. After...
Why Cmmc Compliance Is Forcing Managed It Providers To Rethink Physical SecurityRhode Island has updated its data breach notification law to require faster disclosure, stricter reporting, and full consumer protection. If your business or agency handles resident data, this law applies to you. Learn what changed, why it matters, and how to stay compliant in 2025....
Zero Trust Security And Whitelisting PolicyRhode Island has updated its data breach notification law to require faster disclosure, stricter reporting, and full consumer protection. If your business or agency handles resident data, this law applies to you. Learn what changed, why it matters, and how to stay compliant in 2025....
Secure And Simple Logins With Duo And YubikeyRhode Island has updated its data breach notification law to require faster disclosure, stricter reporting, and full consumer protection. If your business or agency handles resident data, this law applies to you. Learn what changed, why it matters, and how to stay compliant in 2025....
Rhode Island Data Breach Law 2025Massachusetts has updated its data breach notification law with stricter requirements for businesses that collect or store personal data. This update demands faster reporting, confirms who must comply, and outlines what every business needs to do right now to stay protected and avoid penalties. Triton Technologies breaks it down....
Massachusetts Data Breach Notification Law Update 2025